









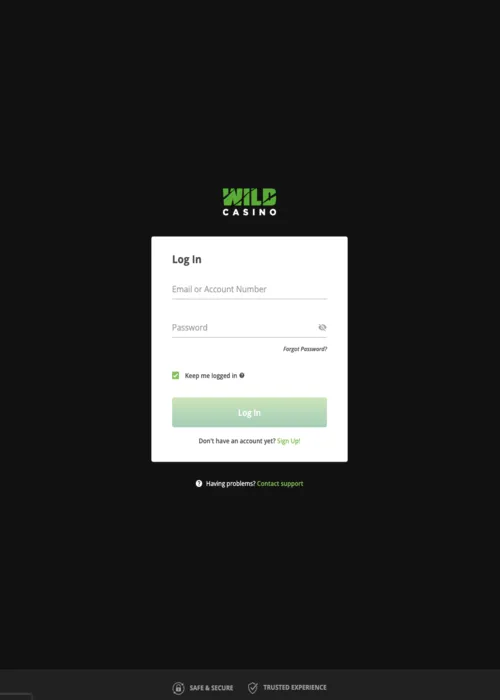
Wild Casino Login – Safe and Private Access to Your Account
At Wild Casino, your login is more than just access—it's the gateway to a fully secured gaming environment. Every sign-in is protected by advanced encryption and multi-factor authentication, ensuring your account, personal data, and VIP privileges remain completely safe. Our platform is built on the principle that a seamless login experience must go hand-in-hand with military-grade security, giving you immediate and trusted access to your favorite games. This robust protection guarantees that all assets, rewards, and account information are shielded while you navigate Wild Casino's dynamic ecosystem.
Advanced Authentication Methods
At Wild Casino, we empower our members with a range of advanced authentication options that extend far beyond traditional credentials. You have the flexibility to integrate biometric verification, such as fingerprint or facial recognition, for a truly seamless and highly secure login experience on compatible devices. For maximum protection, our platform also supports hardware token integration, providing a physical layer of security used by financial and governmental institutions. These smart authentication algorithms are designed to streamline legitimate access while creating an impenetrable barrier against unauthorized attempts.
Multi-Factor Security
We have implemented a mandatory multi-factor security protocol to provide a critical additional layer of protection for every member account. Two-Factor Authentication (2FA) is the modern standard for digital security, and at Casino Wild, it is seamlessly integrated into your login process. You can choose to receive verification codes via SMS, a dedicated authenticator app, or email, ensuring that only you can access your account, even if your password becomes compromised. This system provides a robust defense against unauthorized access, safeguarding your balance and personal information.
Authentication Method Comparison
Choosing the right authentication method is a key part of customizing your security profile. This table provides a clear comparison of the options available at Wild, allowing you to make an informed decision based on your personal preferences for security, speed, and convenience. Each method offers a different balance of these factors, ensuring a suitable option for every member.
| Authentication Method | Security Level | Typical Setup Time | Average Access Speed | Ideal User Profile |
| Password Only | Basic | 1 minute | 5 seconds | Not Recommended |
| 2FA via SMS | High | 3 minutes | 15 seconds | Convenience-focused users |
| 2FA via Authenticator App | Very High | 5 minutes | 10 seconds | Security-conscious users |
| Biometric Verification | Very High | 1 minute | 2 seconds | Mobile-first users |
| Hardware Token | Maximum | 10 minutes | 8 seconds | Ultimate security advocates |
As the data illustrates, while a simple password is fast, its security level is inadequate for the modern digital landscape. We strongly advocate for the use of an authenticator app, as it provides a superior balance of very high security and rapid access. This analysis underscores our commitment at Wild Casino to not only provide options but also to educate our members on making the most secure choices for their accounts.
Session Management
Our platform features an intelligent session management system that actively monitors user activity patterns to detect anomalies and potential security breaches in real-time. To protect you from unauthorized access on unattended devices, we employ automatic session timeouts after a period of inactivity. Furthermore, our secure logout procedures ensure that every session is terminated properly, clearing all sensitive data and providing an additional layer of passive security. This proactive system works silently in the background to protect your account at all times.
Password Security Standards
We enforce a set of advanced password security standards to ensure your primary line of defense is as robust as possible. During the creation or update process, every password undergoes a complexity validation check and is cross-referenced with extensive breach databases to prevent the use of compromised credentials. This is a critical step in the security architecture of Wild site. Real-time password strength meters provide immediate feedback, guiding you to create a password that meets the highest contemporary security standards.
Password Requirements
To ensure the integrity of your account, we have established a clear framework for creating secure passwords. These requirements are not arbitrary; they are based on established cryptographic best practices designed to protect you from common and sophisticated threats. Adhering to these standards is your first and most important step in securing your Wild Casino membership.
- Minimum Length and Complexity: All passwords must be a minimum of 12 characters long and include a combination of uppercase letters, lowercase letters, numbers, and special symbols. This significantly increases the difficulty of brute-force attacks.
- Prohibition of Common Passwords: Our system automatically rejects commonly used passwords (e.g., "password123") and any words found in standard dictionaries, which are frequent targets for attackers.
- Breached Password Check: Before a new password is accepted, it is securely checked against a comprehensive database of credentials known to have been exposed in previous third-party data breaches, ensuring you never use a compromised password.
- Password History Limitation: To prevent credential recycling, our system tracks your password history and prohibits the reuse of your most recent passwords. This is a vital measure for maintaining long-term account security.
- Secure Reset Protocol: Our password reset procedure is a multi-step process requiring verification through a secondary channel, ensuring that only the legitimate account owner can initiate and complete a password change.
These standards work in concert to create a formidable defense for your account. This diligent approach to password security reflects the professional-grade protection you receive at Wild Casino.
Device Management
You have complete control over your account's access points through our integrated device management dashboard. This feature allows you to view and track all devices, desktops, laptops, and mobile phones—that have recently logged into your account. If a device is ever lost, stolen, or simply unrecognized, you have the power to remotely terminate its session and remove its access authorization instantly. This provides you with ultimate control and immediate response capability, ensuring your Wild account remains secure.
Geographic Access Controls
Our security system includes IP-based geographic monitoring to detect and flag unusual login locations. If an access attempt occurs from a new or unexpected region, it automatically triggers an additional verification step to confirm your identity. For your convenience, we also offer a travel notification system. By pre-authorizing access from your planned travel destinations, you can ensure uninterrupted service without compromising the robust security protocols that protect your Wild Casino account.
Security Monitoring
The Wild platform is guarded by a 24/7 security monitoring system that operates in real-time. We utilize advanced fraud detection algorithms that analyze login patterns, device fingerprinting, and behavioral biometrics to identify potential threats with incredible accuracy. Should a high-risk activity be detected, our system's automated security responses are initiated immediately. These can include a temporary account lockout, a mandatory verification challenge, and instant notifications sent directly to you, ensuring threats are neutralized proactively.
Access Recovery Procedures
In the event you are unable to access your account, we have established comprehensive and secure recovery procedures designed to verify your identity and restore access efficiently. We understand that forgetting a password or losing access to a 2FA device can happen, and our system is built to handle these scenarios without compromising your account's integrity. These multi-step verification pathways ensure that only the legitimate owner of the Wild Casino account can regain control.
Recovery Method Options
To accommodate various member circumstances, our access recovery protocol includes multiple verification pathways. The primary method involves a rigorous identity verification process, which may require submitting a valid government-issued ID that is cross-referenced with your account details. Alternative recovery paths include secure links sent to your registered email, confirmation codes delivered via SMS, and answering pre-selected security questions to which only you know the answers. This layered approach ensures a secure and reliable recovery process.
Login Optimization
At Wild, we believe that robust security should not come at the expense of convenience. Our login process is optimized with smart features designed to streamline your access. These include secure credential saving options for trusted devices, browser auto-complete compatibility, and seamless biometric recognition. By leveraging these technologies, we reduce friction and allow you to access your account quickly and efficiently, perfectly balancing state-of-the-art security with a superior user experience.
Security Education
We view our members as partners in maintaining a secure gaming environment. Wild Casino provides a comprehensive security awareness program to educate you about the latest cyber threats, including phishing scams, social engineering tactics, and malware risks. Through our security center, we offer regular updates, actionable tips, and best practices. This educational initiative empowers you with the knowledge to identify potential threats and maintain optimal account protection, reinforcing the security of our entire community.
Audit Trail Maintenance
For complete transparency and security, the Wild Casino platform maintains a detailed and immutable audit trail of all account activities. Every login attempt, successful authentication, password change, and other significant security event is meticulously logged with a timestamp, IP address, and device identifier. This information is accessible to you through your personal security dashboard, providing a clear and comprehensive history of your account access. This level of transparency gives you the power to monitor your own account's security and demonstrates our unwavering commitment to member protection and operational integrity.
